Legal aspects of criminology
Sorting
Bestseller Sorting collapsed
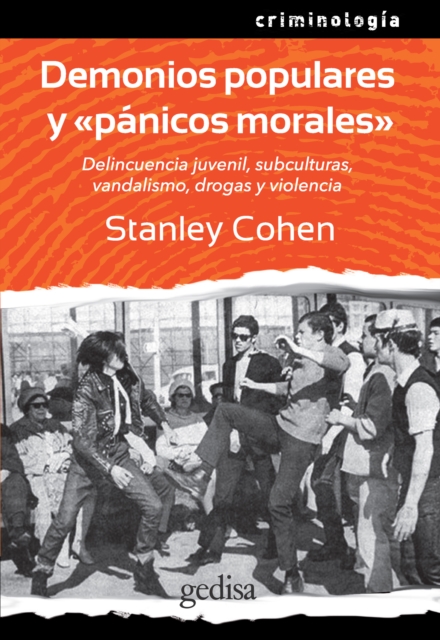
E-book
Price
10.82 £ * Old Price 12.99 £
E-book
Price
10.82 £ * Old Price 12.99 £
E-book
Price
14.16 £ * Old Price 16.99 £
E-book
Price
28.32 £ * Old Price 33.99 £
E-book
Price
10.82 £ * Old Price 12.99 £
E-book
Price
3.74 £ * Old Price 4.49 £
E-book
Price
21.66 £ * Old Price 25.99 £